Threat Watch
Unlock your cybersecurity potential with instant insights that safeguard your digital assets.
AI tool Details
Explore More
Alternatives
About Threat Watch
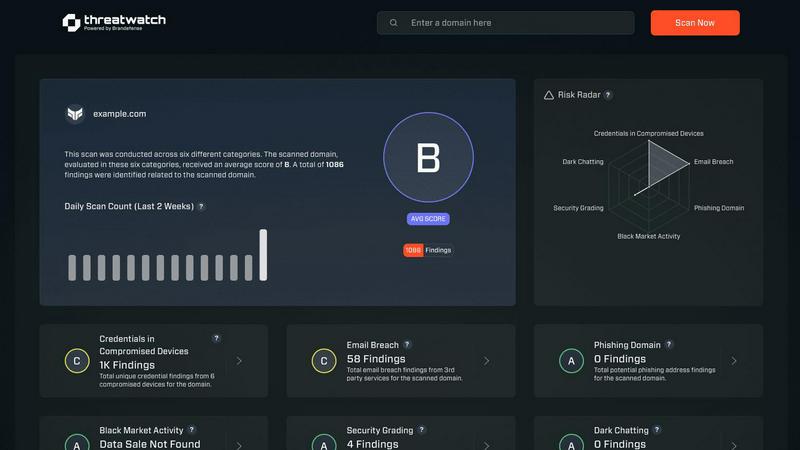
In today's hyper-connected digital ecosystem, reactive security is a recipe for disaster. Threat Watch is the game-changing cybersecurity intelligence platform that shifts the paradigm from defense to proactive dominance. This transformative solution is engineered to empower organizations, IT professionals, and security teams with a crystal-clear, real-time view of their cyber health. It meticulously scans and analyzes the most critical threat vectors, including compromised credentials, breached accounts, phishing addresses, and dark web exposures, consolidating them into a single, actionable dashboard. By unlocking this intelligence, Threat Watch enables you to identify, prioritize, and neutralize risks with unprecedented speed and accuracy before they escalate into full-blown incidents. Its core value proposition is delivering peace of mind through automated, continuous assessment, allowing you to fortify your digital perimeter and focus strategic resources on innovation and growth, secure in the knowledge that your assets are protected.
Features
Comprehensive Cyber Health Dashboard
Unlock an instant, panoramic view of your organization's security posture with our transformative dashboard. This centralized command center aggregates data from all critical security categories, presenting a clear, visual score of your cyber health. It translates complex threat data into intuitive insights, enabling you to see your vulnerabilities at a glance and track improvements over time, transforming raw data into strategic intelligence.
Real-Time Compromised Credentials Monitoring
Go beyond periodic checks with continuous, real-time surveillance for exposed employee credentials across data breaches, paste sites, and the dark web. This feature proactively alerts you the moment a username or password associated with your domain is discovered, allowing you to enforce immediate password resets and prevent account takeover attacks before they begin, fundamentally changing your breach response time.
Automated Dark Web & Breach Surveillance
Our platform automates the tedious and complex task of scanning the dark web and underground forums for mentions of your organization, leaked data, and breached accounts. This game-changing feature provides automated alerts when your corporate information appears in illicit markets, giving you a critical head start to mitigate damage and protect your reputation from unseen threats.
Phishing Address & Domain Intelligence
Proactively identify and neutralize phishing risks by discovering email addresses mimicking your legitimate domains that are being used in active campaigns. Threat Watch scans for these fraudulent addresses and compromised devices within your network, providing the intelligence needed to take down malicious sites and educate users, effectively shutting down a primary attack vector.
Use Cases
Proactive IT & Security Team Empowerment
Security teams are transformed from fire-fighters to strategic advisors. Threat Watch provides them with automated, evidence-based risk reports, allowing them to prioritize patching, guide user training, and justify security investments with hard data. This shifts their role to proactive threat hunting and strategic planning, unlocking their full potential to defend the organization.
Executive & Board-Level Risk Reporting
Provide C-suite executives and board members with clear, concise, and non-technical reports on the organization's cyber health score and exposure levels. This use case transforms complex security data into business risk intelligence, enabling informed decision-making and demonstrating due diligence in cybersecurity governance and compliance.
Rapid Post-Breach Impact Assessment
In the critical aftermath of a third-party data breach, quickly determine if your organizational data or employee credentials were exposed. Threat Watch allows you to rapidly assess the scope of impact, identify which specific accounts are compromised, and take immediate, targeted action to secure them, minimizing operational downtime and financial loss.
Enhanced Vendor & Third-Party Risk Management
Extend your security monitoring to evaluate the cyber health of critical partners and vendors. By assessing whether vendor credentials or domains appear in breaches, you can identify weak links in your supply chain. This empowers you to have data-driven conversations about security requirements and mitigate risks originating from outside your direct control.
Frequently Asked Questions
How does Threat Watch discover my company's exposed data?
Threat Watch operates by continuously monitoring a vast array of data sources, including public data breaches, private underground forums, paste sites, and dark web marketplaces. Our system uses your organization's domains and other identifiers to scan these sources in real-time, alerting you immediately when matching credentials, internal IPs, or other sensitive data is found exposed.
Is a free scan truly free, and what does it include?
Yes, the initial cyber health scan is completely free and requires no credit card. This scan provides a valuable snapshot of your organization's exposure across key categories like compromised credentials and breached accounts. It delivers a report highlighting found risks, giving you immediate insight into your security posture without any obligation.
What makes Threat Watch different from a standard antivirus?
While antivirus software protects endpoints from known malware files, Threat Watch operates on an intelligence and prevention layer. It focuses on external digital risks like stolen credentials and phishing setups before they can be used to launch an attack that antivirus would need to detect. It's a proactive early-warning system, not just a reactive defense.
How quickly will I be alerted if a new threat is found?
Threat Watch is designed for real-time intelligence. The platform provides immediate, automated alerts through your dashboard and can be configured to send email notifications the moment a new, critical exposure is detected. This ensures your team is informed with the speed necessary to respond to fast-moving threats effectively.
Similar to Threat Watch
FX Radar
FX Radar delivers real-time forex and financial news in seconds, empowering traders with powerful tools to analyze and optimize their performance.
AI Business Name Generator
Transform your business vision into reality with unique and memorable names generated instantly by our AI Business Name Generator.
MarketWrk
MarketWrk automates pricing and MAP monitoring to transform raw data into actionable intelligence instantly.
Opal44
Opal44 transforms your website traffic data into clear, actionable insights with AI-powered simplicity and no jargon.
Fusedash
Fusedash transforms raw data into clear dashboards so teams can act on insights instantly.
finban
finban is your liquidity OS, transforming cash flow chaos into confident, data-driven decisions.
Zignt
Zignt revolutionizes contract signing with unlimited templates and instant, legally binding e-signatures delivered.
RoomX AI - Virtual Staging in 30 Seconds
Transform vacant listings into buyer magnets with AI virtual staging in just 30 seconds.