Hush Touch | Voice-to-Text for MacOS vs RedVeil
Side-by-side comparison to help you choose the right AI tool.
Hush Touch | Voice-to-Text for MacOS
Experience smarter on-device dictation for Mac, transforming speech into text with unmatched accuracy and privacy.
Last updated: February 28, 2026
RedVeil
RedVeil delivers on-demand AI penetration testing to uncover real vulnerabilities at unprecedented speed.
Last updated: February 28, 2026
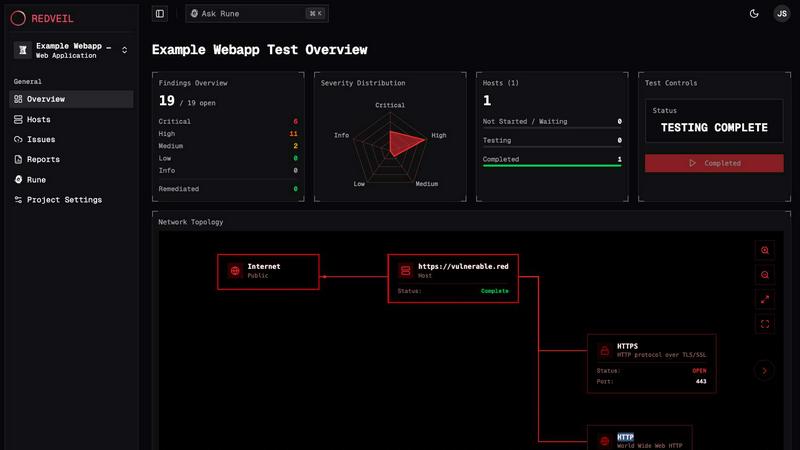
Visual Comparison
Hush Touch | Voice-to-Text for MacOS

RedVeil
Feature Comparison
Hush Touch | Voice-to-Text for MacOS
Dual-Engine Recognition
Hush Touch employs a unique dual-engine recognition system that combines DictationTranscriber and SFSpeechRecognizer. This allows for natural flow and accurate punctuation while also understanding and incorporating your custom vocabulary. By blending these two powerful Apple engines, the app delivers unparalleled accuracy and responsiveness in real-time dictation.
Custom Vocabulary
Hush Touch supports a custom vocabulary feature that allows users to add up to 500 terms. This is especially beneficial for professionals in specialized fields such as medicine or technology, where specific jargon is common. The app learns from corrections you make during dictation, adapting to your unique language preferences over time.
Smart Text Processing
The app's smart text processing capabilities enhance the dictation experience by removing filler words, auto-correcting common mistakes, and formatting text as you dictate. Voice snippets for repeated phrases and numbered list formatting are processed locally and in real-time, ensuring a smooth and efficient writing experience without interruptions.
100% On-Device Privacy
With Hush Touch, your privacy is paramount. The app processes all voice data locally on your Mac, eliminating any reliance on cloud services. This means zero data collection and complete control over your information, providing peace of mind while dictating sensitive content.
RedVeil
Autonomous AI Attack Agents
RedVeil deploys intelligent AI agents trained to reason and execute multi-step attack chains just like a human adversary. These agents don't just run simple scans; they dynamically explore, exploit, and connect vulnerabilities to uncover deep attack paths, providing a realistic assessment of your security posture with the depth of a manual test.
On-Demand Testing & One-Click Retesting
Eliminate the scheduling delays and scoping calls of traditional pentests. With RedVeil, you can initiate a full penetration test whenever you need it—in minutes. The revolutionary One-Click Retesting feature allows you to validate fixes immediately after remediation, enabling a true continuous security loop at the speed of your development.
Compliance-Ready Reporting Engine
Generate professional, detailed reports tailored for executives, engineers, and auditors with a single click. RedVeil's reporting is specifically formatted to meet the evidence requirements of major compliance frameworks like SOC 2, ISO 27001, and PCI-DSS, delivering them in hours instead of weeks to streamline your audit process.
Guided Remediation with Rune
Rune is your embedded security expert, providing unparalleled clarity and support throughout the testing lifecycle. It assists with scope setup, breaks down complex findings into plain language, and offers step-by-step remediation guidance to ensure your team can effectively understand and fix every identified vulnerability.
Use Cases
Hush Touch | Voice-to-Text for MacOS
Drafting Emails
Hush Touch is an excellent tool for busy professionals looking to draft emails quickly and efficiently. With hands-free dictation and customizable command phrases, users can send messages seamlessly without the need to type, allowing for more focus on the content of the email.
Taking Notes
Students and professionals alike can benefit from Hush Touch when taking notes during lectures or meetings. The ability to dictate notes in real-time allows for a more natural flow of information and ensures that important details are captured effortlessly, enhancing productivity.
Writing Documents
Whether it's a report, article, or creative writing piece, Hush Touch transforms the writing process. Users can dictate entire documents without the constraints of traditional typing, fostering creativity and allowing thoughts to flow freely.
Coding and Technical Writing
For software developers and technical writers, Hush Touch’s dual-engine recognition is invaluable. The app can accurately transcribe complex terminology and code commands, making it easier to document processes or communicate technical concepts without the hassle of typing.
RedVeil
Continuous Compliance Validation
Organizations needing to maintain SOC 2, ISO 27001, or PCI-DSS compliance can use RedVeil to perform regular, on-demand penetration tests. This provides continuous evidence of security controls, fills gaps between annual manual audits, and ensures you are always prepared for an auditor's review without last-minute scrambles.
Agile & DevOps Security Integration
Development teams practicing CI/CD can integrate RedVeil into their release cycles. By running autonomous pentests against staging or production environments after major deployments, they can identify and remediate critical security flaws before they impact users, enabling true DevSecOps and shifting security left.
Pre-Merger & Acquisition Due Diligence
Companies undergoing M&A activities can rapidly assess the security posture of a target acquisition. RedVeil provides a fast, thorough, and independent analysis of external and internal attack surfaces, delivering a clear risk assessment report to inform critical business decisions within tight timelines.
Proactive Risk Management for Growing Businesses
Growing startups and mid-market companies that lack a large in-house security team can leverage RedVeil as their force multiplier. It offers enterprise-grade security testing on-demand, allowing them to proactively manage risk, secure new features, and protect their expanding digital footprint predictably.
Overview
About Hush Touch | Voice-to-Text for MacOS
Hush Touch is a revolutionary voice-to-text application designed specifically for macOS, prioritizing natural dictation, speed, and privacy. Ideal for professionals, writers, and anyone who values efficient communication, Hush Touch operates entirely on-device, ensuring that your voice data remains secure and private. With a lightweight installation of just 5.5 MB, it launches quickly and integrates seamlessly into your daily writing processes. The app utilizes two advanced Apple transcription engines combined with an Apple Intelligence final pass, resulting in remarkably accurate and clean text output. Users can easily dictate emails, notes, and documents hands-free, thanks to customizable command phrases and smart auto-insertion features. Hush Touch is perfect for those seeking a dependable dictation solution without reliance on cloud services, making it an essential tool for anyone who values both privacy and efficiency in their workflow.
About RedVeil
RedVeil is a game-changing AI-powered penetration testing platform that shatters the traditional security assessment model. It is engineered for modern engineering and security teams who can no longer afford the slow, expensive, and infrequent cycles of manual pentesting. By operationalizing penetration testing, RedVeil delivers the strategic reasoning of a human hacker with the unprecedented speed and scalability of autonomous AI software. This transformative approach allows organizations to spin up a comprehensive, full-scope penetration test in mere minutes and receive a detailed, actionable, and audit-ready report within hours—not weeks. It’s built for teams that deploy code daily, offering a new standard of continuous security validation that aligns with agile development cycles. RedVeil empowers businesses to proactively uncover and remediate exploitable risks on-demand, ensuring their defenses evolve as fast as their attack surface does, all at a predictable and accessible price point.
Frequently Asked Questions
Hush Touch | Voice-to-Text for MacOS FAQ
How does Hush Touch ensure privacy?
Hush Touch guarantees privacy by processing all voice data entirely on your Mac. There is no reliance on cloud services or external servers, ensuring your information remains confidential and secure.
Can I customize the vocabulary?
Yes, Hush Touch allows users to add up to 500 custom terms to its vocabulary. It learns from your corrections, adapting to your specific language needs and improving accuracy over time.
Is there a trial available for Hush Touch?
Absolutely! Hush Touch offers a 7-day free trial with no credit card required. You can experience the app's functionality and performance firsthand before making a purchase.
What is the cost of Hush Touch?
Hush Touch is available for a one-time payment of $20, providing users with a lifetime license. This eliminates the need for monthly subscriptions, making it a cost-effective solution for voice-to-text dictation.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes, absolutely. RedVeil is not a simple vulnerability scanner. It conducts authentic penetration tests using autonomous AI agents that reason through multi-step attack chains, exploit identified vulnerabilities, and provide evidence of real, exploitable risks—mimicking the methodology and depth of a skilled human ethical hacker.
How many penetration tests can I do with my annual subscription?
Your subscription includes an annual allocation of "Agent Ops," which are units of testing effort. You can use these Ops to run multiple tests throughout the year. For example, the Perimeter plan includes 500 Agent Ops annually, allowing for several full tests or more frequent, smaller-scope assessments, giving you complete flexibility.
Can I use RedVeil's reports for compliance audits?
Yes. RedVeil generates professional, audit-ready reports specifically designed to meet the requirements of major compliance frameworks such as SOC 2, ISO 27001, and PCI-DSS. These reports include detailed findings, evidence, and remediation guidance that auditors expect to see.
What if I have concerns about submitting my report to my auditor?
RedVeil's reports are built to provide clear, professional, and validated evidence. For additional assurance, you can contact their team. The structured format and detailed exploitation evidence within the reports are crafted to give both you and your auditor confidence in the findings and the testing methodology.
Alternatives
Hush Touch | Voice-to-Text for MacOS Alternatives
Hush Touch | Voice-to-Text for MacOS is an innovative voice-to-text application designed specifically for macOS users. It leverages advanced on-device processing, utilizing two Apple transcription engines followed by an Apple Intelligence final pass, ensuring faster and more accurate text conversion without the need for internet connectivity. As part of the AI Assistants category, it caters to individuals seeking seamless dictation experiences. Users often seek alternatives to Hush Touch due to various reasons, including pricing, feature sets, compatibility with different platforms, and specific user requirements. When selecting an alternative, it's essential to consider factors such as ease of use, the ability to work offline, transcription accuracy, and how well the software integrates into existing workflows. Additionally, assessing privacy measures and overall cost-effectiveness can significantly influence the decision-making process.
RedVeil Alternatives
RedVeil is a pioneering agentic AI platform that delivers on-demand penetration testing. It belongs to the category of AI-driven security tools designed to automate the complex, reasoning-based work of human security experts. This innovative approach makes continuous security validation accessible and practical for modern development teams. Users often explore alternatives for various reasons, such as budget constraints, specific feature requirements, or integration needs with their existing tech stack. Some may seek tools with a different focus, like purely manual testing for compliance, or platforms that offer broader vulnerability management beyond automated pentesting. When evaluating options, key considerations include the depth and accuracy of findings, the speed and automation of the testing cycle, compliance reporting capabilities, and overall cost-effectiveness. The ideal solution should align with your team's deployment velocity and provide actionable, audit-ready intelligence without creating bottlenecks.
